ISO 27001 and SOC 2: What They Are, Why You Need One & How Not to Do It Badly

This usually starts with an email you were not planning for. A client asks if you are ISO 27001 certified. An investor drops SOC 2 into a due diligence checklist. Procurement assumes you already have both.
Very rarely does anyone explain why. You are simply expected to have it.
At this point, many organisations panic. They start searching online. They find companies promising ISO 27001 certification in a matter of days for very little money. They download templates. They create documents nobody will ever read.
And somehow, things feel worse than before.
This article cuts through that confusion. It explains what ISO 27001 and SOC 2 actually are, why people ask for them, where they overlap, and how to approach them properly without turning security into a box-ticking exercise.

Why Clients and Investors Ask for ISO 27001 or SOC 2
People rarely ask for ISO 27001 or SOC 2 because they like standards. They ask because they want assurance.
From their perspective, they are trying to answer a simple question.
Can we trust you with our data, our systems, or our reputation?
ISO 27001 and SOC 2 have become shorthand ways of answering that question without deeply auditing every supplier. They indicate that you have thought about security risk, put controls in place, assigned ownership, and had your approach reviewed independently.
That is why investors include them. That is why clients ask for them. It is not about perfection. It is about reducing uncertainty.
ISO 27001 and SOC 2 in Plain English
What ISO 27001 Actually Is?
ISO 27001 is an information security management system standard. In practical terms, it is a structured way to identify security risks, decide how to treat them, assign responsibility, and review whether controls are actually working.
It is not a list of mandatory tools. It is not a technical checklist. It is a management system.
At its core, ISO 27001 asks:
- What are your information security risks?
- Which ones matter most?
- What controls have you chosen and why?
- Who owns them?
- How do you know they are working?
What SOC 2 Actually Is?
SOC 2 is an assurance report, not a management system. It is designed to provide third parties with confidence that specific controls are designed appropriately and operating effectively.
SOC 2 focuses on trust service criteria such as security, availability, and confidentiality. It is commonly used by technology providers and service organisations, particularly where clients want formal assurance without running their own audits
SOC 2 Type 1 vs Type 2
This catches a lot of people out.
- Type 1 shows that controls exist at a point in time
- Type 2 shows that controls operated effectively over a defined period, usually six to twelve months
Type 2 is what most clients actually care about, but it takes time and evidence to achieve.
Timescales: Why This Is Not a Quick Win
If someone promises ISO 27001 certification in a few days, that should raise questions.
Doing this properly takes time because it involves understanding your environment, identifying real risks, embedding controls, generating evidence, and reviewing and improving.
A realistic timeline is measured in months, not days. Anything faster is usually paperwork without substance.
What an ISMS Really Is (And What It Is Not)

An Information Security Management System is not:
- A SharePoint folder full of policies
- A one-off project
- A spreadsheet nobody maintains
An ISMS is a living system. It evolves as your business changes. People join and leave. Systems change. Risks shift.
If your ISMS cannot cope with that, it will collapse under its own weight.
The Five-Day ISO Certification Trap
This is worth being blunt about.
If your ISO 27001 certificate is not issued by a certification body accredited by either UKAS for the UK and EMEA, or ANAB for the United States, then in my opinion it is not worth having.
Many buyers know this. Auditors know this. Investors know this.
Cheap, fast certification usually means:
- Generic templates
- Minimal risk assessment
- No meaningful assurance
- Problems later when someone looks closely
You may technically have a certificate, but you will still struggle when a client asks sensible follow-up questions.
ISO 27001 and SOC 2: The Overlap That Makes Life Easier
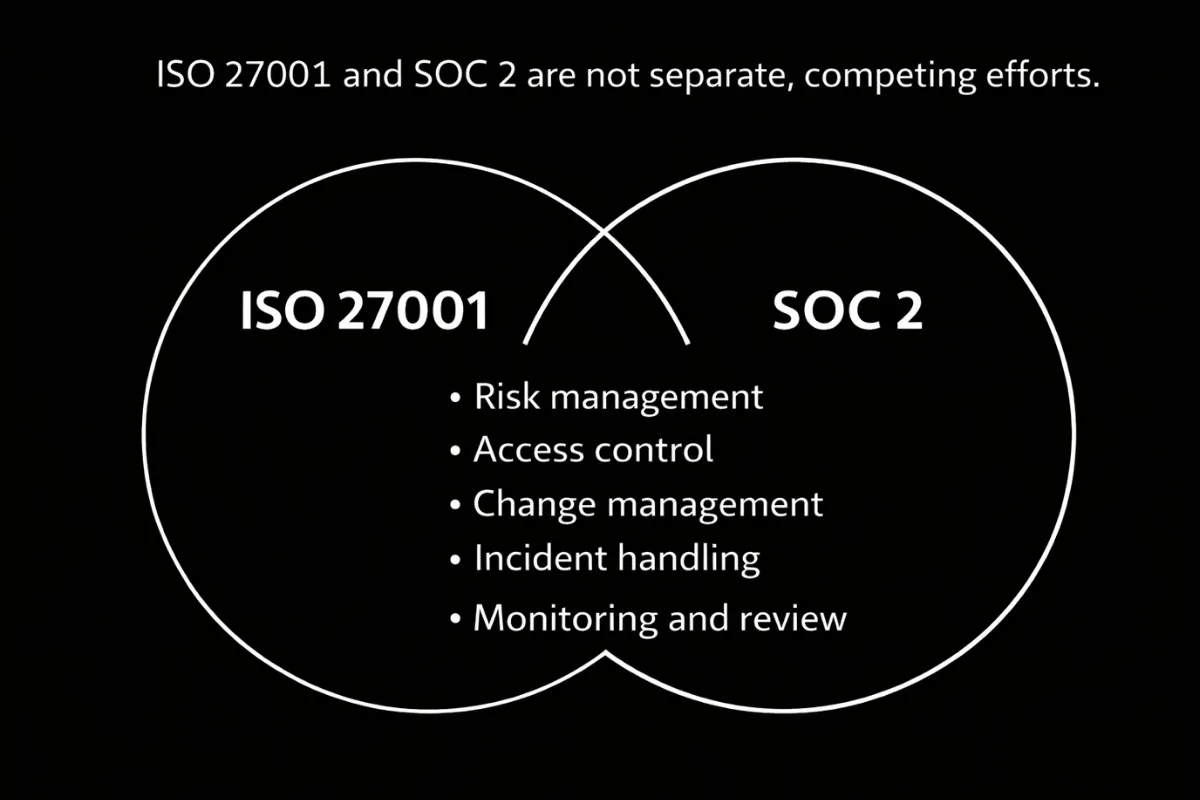
The good news is that ISO 27001 and SOC 2 overlap significantly.
Both focus on:
- Risk management
- Access control
- Change management
- Incident handling
- Monitoring and review
If you approach this sensibly, you do not build two separate programmes. You build one strong foundation and map it to both.
How to Do This Without Drowning Every Year
Yes, you can manage an ISMS in Excel. Many organisations do. For a while.
- Then people leave
- Tabs get duplicated
- Evidence goes missing
- Nobody trusts the data anymore.
That is why purpose-built compliance tools exist.

They help to:
- Track ownership
- Automate evidence collection
- Keep risk registers current
- Present cleanly to auditors
- Reduce repeated questions when you are already busy
They are not cheap, but neither is lost time, audit pain, or rework. In practice, they usually pay for themselves quickly.
Common Mistakes We See Repeatedly
- Treating ISO 27001 or SOC 2 as a one-off exercise
- Chasing certification rather than capability
- Over-documenting and under-operating
- Ignoring how the business actually works
- Leaving everything with one overwhelmed person
These mistakes create fragile programmes that look fine on paper and fall apart under scrutiny.
Frequently Asked Questions
Do I need ISO 27001 or SOC 2?
It depends who is asking and why. Many organisations end up needing both over time, but not always at once.
Can I start with ISO 27001 and add SOC 2 later?
Yes. This is often the most sensible route.
Is certification the goal?
Certification is a by-product. The real goal is trust and risk reduction.
Conclusion
ISO 27001 and SOC 2 are not about jumping through hoops. They are about demonstrating that security is managed, risks are understood, and decisions are made deliberately rather than reactively.
When approached properly, they reduce long-term effort and build trust. When rushed or treated as paperwork, they create ongoing pain.
How Onion Security Helps
This is usually the point where organisations realise the issue is not effort, but direction. Onion Security helps organisations approach ISO 27001 and SOC 2 pragmatically. Not by rushing to certification, but by building something that actually works, stands up to scrutiny, and does not collapse a year later.
The focus is on real risks, sensible controls, and systems that reduce long-term effort rather than increasing it.
Cyber Security Solutions
Delivering a robust cyber security posture that withstands any threat











