Penetration Testing: Why a Fancy Scan Is Not the Same Thing & Why It Still Matters

Penetration testing is one of the most misunderstood activities in cyber security. Many organisations believe they already do it. They run vulnerability scans. They get a report with charts, colours, and risk scores. They feel reassured.
Others assume they do not need it at all.
- We are not a target
- We do not hold anything worth stealing
- If something happens, we have backups
These assumptions are common. They are also responsible for many avoidable incidents.
Penetration testing exists to answer a much harder and more uncomfortable question.
If someone wanted to break in, could they actually do it, and what would happen next?
This article explains what penetration testing really is, how it differs from vulnerability scanning, why it matters even for organisations that think they are low risk, and what the real consequences are when it is ignored.
What Penetration Testing Actually Means
Penetration testing is the controlled simulation of a real attack. It involves skilled testers attempting to exploit weaknesses in systems, applications, or networks in the same way a real attacker would, but in a safe and agreed manner.
The goal is not to find every vulnerability.
The goal is to understand impact.
A good penetration test shows:
- What an attacker could realistically access
- How weaknesses can be chained together
- Whether security controls actually work
- What the business impact would be
This is very different from producing a long list of technical findings.
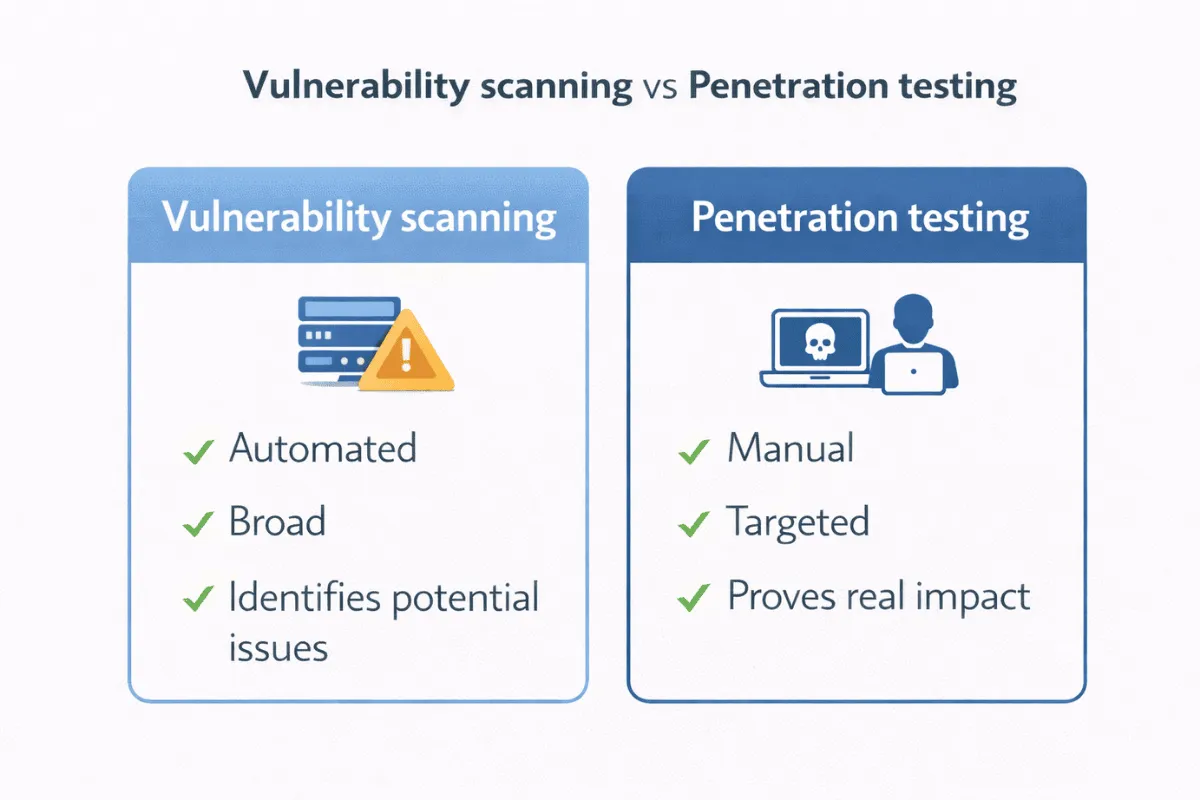
Penetration Testing Versus Vulnerability Scanning
This is where a lot of confusion comes from. Vulnerability scanning is automated. It looks for known issues such as missing patches, weak configurations, or exposed services.
Penetration testing is manual and analytical. It looks at whether those issues can actually be exploited.
- A scan might tell you a door is unlocked
- A penetration test tells you whether someone can walk through it, where they end up, and what they can touch once inside
- Both have value, but they answer different questions.
Scanning is about coverage. Penetration testing is about realism.
Why Free Scans and Fancy Reports Create False Confidence
Many organisations rely on free or low-cost scanning tools that generate attractive reports.
These tools are useful, but they come with limitations.
- They do not understand business context
- They do not chain weaknesses together
- They do not think creatively
- They do not validate impact.
This often leads to two dangerous outcomes. Either teams become overwhelmed by volume and fix nothing meaningful, or they see no critical findings and assume everything is fine.
Neither outcome improves security.
"We Are Not a Target” Is Rarely True
Attackers do not target organisations because they are famous.
They target them because they are easy.
Automated attacks scan the internet continuously looking for weaknesses. Many breaches start without any prior knowledge of who the victim is.
Even organisations that do not hold obvious high-value data are attractive because:
- They can be used as a stepping stone to others
- They have access to third parties or customers
- They can be disrupted for ransom
- They trust their internal networks too much
Being small or quiet does not make you invisible.
Why Backups Do Not Save You From the Real Damage
Backups are important, but they are not a get-out-of-jail-free card.
Penetration testing often reveals risks that backups do not address.
These include:
- Theft of credentials or sensitive data
- Manipulation of systems rather than destruction
- Loss of trust from customers and partners
- Regulatory scrutiny
- Operational disruption during investigation and recovery
Even if systems are restored, the business impact can last far longer.
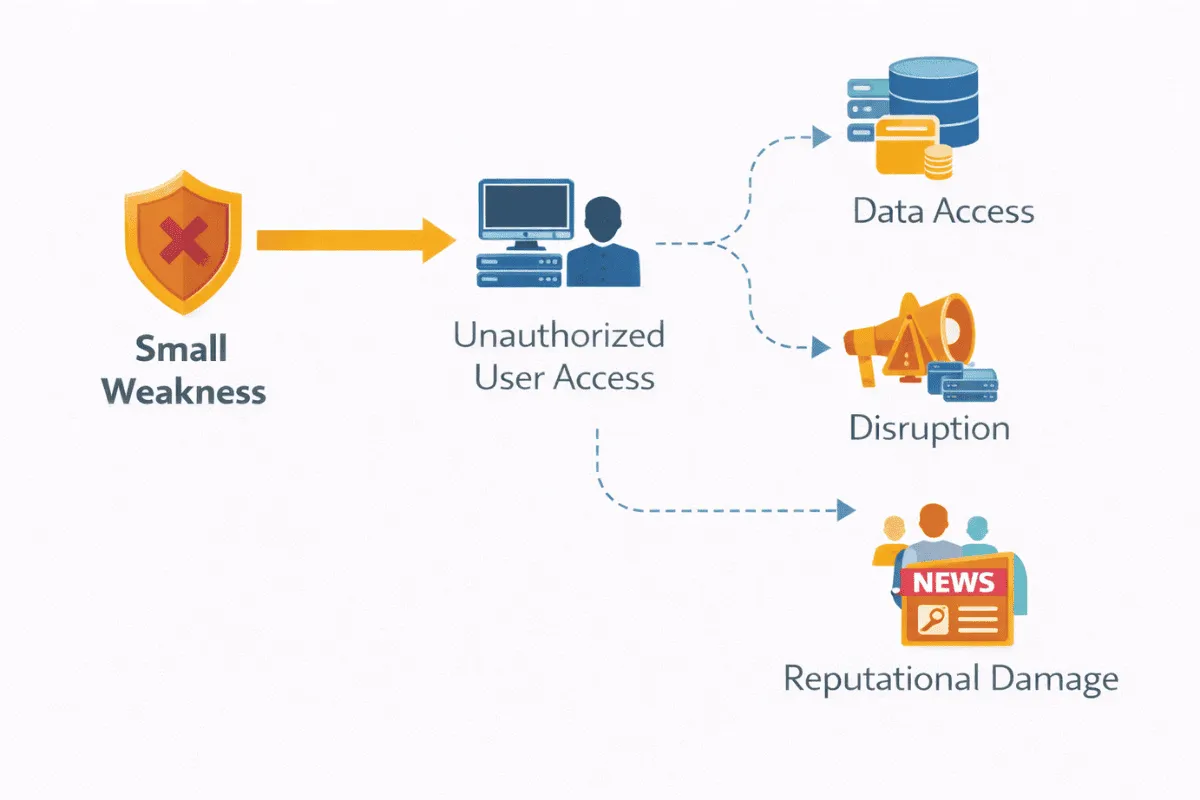
The Real Cost of a Breach Is Not Technical
When organisations talk about breaches, they often focus on technical recovery. In practice, the most damaging effects are usually non-technical.
- Reputational damage can kill deals overnight
- Customers may lose confidence
- Partners may suspend access
- Third parties may lock you out of shared systems.
Once trust is lost, restoring it is far harder than restoring servers.
How Penetration Testing Fits With Resilience
Penetration testing and resilience are closely linked.
Testing shows how an incident could start.
Resilience determines how well you cope when it does.
Penetration testing helps organisations understand:
- Which systems would be compromised first
- How quickly an attacker could move
- What controls fail under pressure
- Where recovery and containment would be hardest
Without this insight, resilience planning is often based on guesswork.

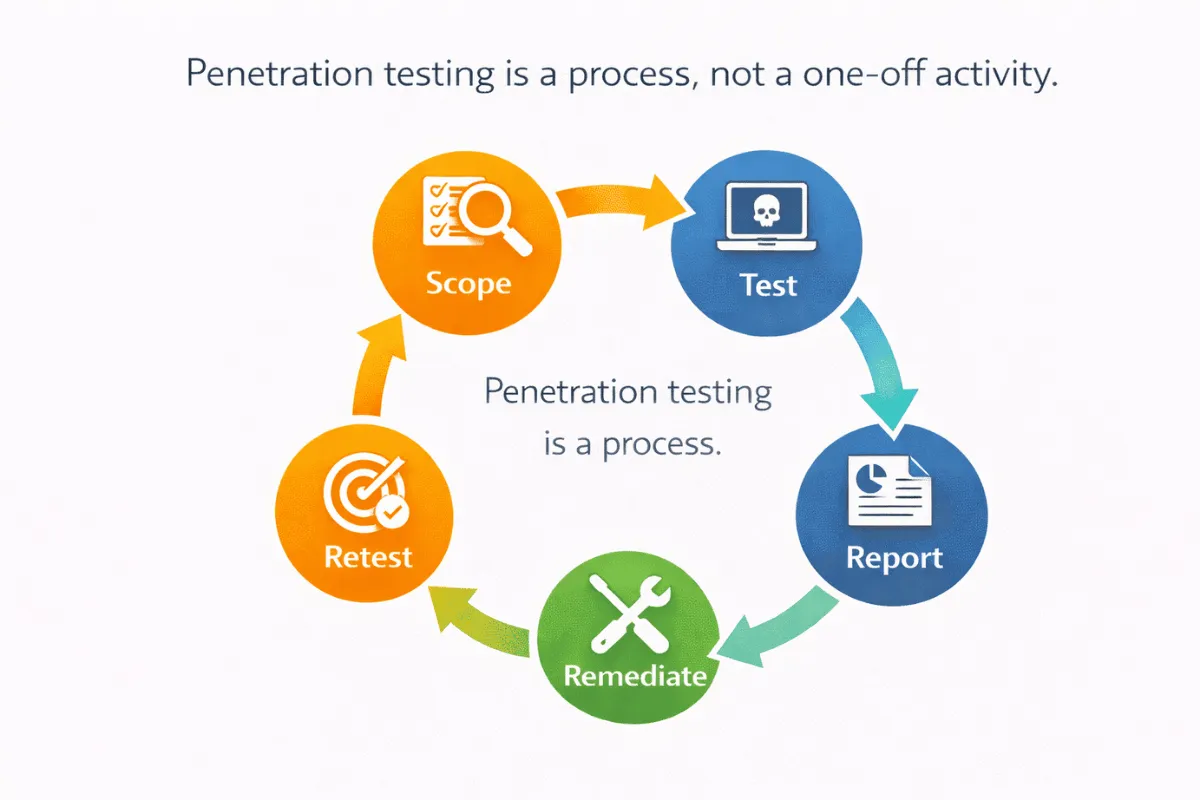
How Often Should Penetration Testing Be Done
There is no single correct frequency. Testing should be driven by risk and change, not by calendar dates alone.
Situations that usually justify testing include:
- New internet-facing systems or applications
- Major changes to authentication or access control
- Cloud migrations or platform changes
- Significant architectural changes
- After a serious incident
For critical systems, regular testing is part of maintaining confidence, not a one-off exercise.
Common Penetration Testing Mistakes We See
- Treating it as a compliance checkbox
- Scoping tests too narrowly to avoid findings
- Ignoring business impact in reports
- Failing to retest after fixes
- Leaving findings open for months
- Not linking results to risk decisions
These mistakes turn a valuable activity into wasted effort.
Frequently Asked Questions
Is penetration testing mandatory?
It is not always explicitly mandated, but it is widely expected where systems are internet facing, sensitive, or business critical.
How is penetration testing different from red teaming?
Penetration testing focuses on specific systems and controls. Red teaming focuses on end-to-end attack scenarios and organisational response.
Should penetration testing include social engineering?
Sometimes. It depends on risk, maturity, and objectives. It should always be carefully scoped.
Conclusion
Penetration testing is not about proving how clever attackers are. It is about understanding where assumptions break down. When done properly, it provides clarity rather than fear. It helps organisations prioritise effort, improve resilience, and make informed decisions about risk.
When skipped or reduced to a scan, it creates false confidence and surprises later.
How Onion Security Helps
Penetration testing is most effective when it is used to support decisions rather than tick a box. Onion Security helps organisations scope testing sensibly, focus on real risk, and translate technical findings into clear actions the business understands.
The aim is not to generate noise. It is to reduce uncertainty and prevent small weaknesses from becoming serious incidents.
Cyber Security Solutions
Delivering a robust cyber security posture that withstands any threat











